Difference between revisions of "1957: 2018 CVE List"
(Undo revision 184302 by 172.69.194.4 (talk) Let's not make them protect the page, okay? That doesn't seem very related.) |
(Language) |
||
| (51 intermediate revisions by 36 users not shown) | |||
| Line 19: | Line 19: | ||
:The reference to using a Timing Attack to exploit a race condition in garbage collection refers to Meltdown and Spectre CPU flaws that can be exploited in a cloud server like the ones in Wikipedia. {{w|Claude Shannon}} was an early and highly influential information scientist whose work underlies compression, encryption, security, and the theory behind how information is encoded into binary digits. | :The reference to using a Timing Attack to exploit a race condition in garbage collection refers to Meltdown and Spectre CPU flaws that can be exploited in a cloud server like the ones in Wikipedia. {{w|Claude Shannon}} was an early and highly influential information scientist whose work underlies compression, encryption, security, and the theory behind how information is encoded into binary digits. | ||
: | : | ||
| − | :This is not a security problem. However, since Shannon formulated how the amount of unique or actual information some entity contains is proportional to the number of bits required to encode it, retrieving only a few bits casts a dark perspective upon the significance of the Shannon article's content. | + | :This is not a security problem, since Wikipedia articles are public. However, since Shannon formulated how the amount of unique or actual information some entity contains is proportional to the number of bits required to encode it, retrieving only a few bits casts a dark perspective upon the significance of the Shannon article's content. |
;At the cafe on Third Street, the Post-it note with the WiFi password is visible from the sidewalk. | ;At the cafe on Third Street, the Post-it note with the WiFi password is visible from the sidewalk. | ||
| − | :Cafés often offer free access to WiFi as a service to patrons, as a business strategy to encourage said patrons to remain in the building and buy more coffee. Some use a password, so that only patrons can use the WiFi, and may display the password on signage inside. Since anybody could go into the cafe to read the post-it, and then use the network from nearby, the ability to read it from outside is, at most, a trivial problem. For systems that are supposed to be secure, writing passwords in a visible place is a major security flaw. For instance, following the [[wikipedia:2018 Hawaii false missile alert|2018 Hawaii false missile alert]], the agency concerned received criticism for a press photo showing [ | + | :Cafés often offer free access to WiFi as a service to patrons, as a business strategy to encourage said patrons to remain in the building and buy more coffee. Some use a password, so that only patrons can use the WiFi, and may display the password on signage inside. Since anybody could go into the cafe to read the post-it, and then use the network from nearby, the ability to read it from outside is, at most, a trivial problem. For systems that are supposed to be secure, writing passwords in a visible place is a major security flaw. For instance, following the [[wikipedia:2018 Hawaii false missile alert|2018 Hawaii false missile alert]] (see [[Hawaii]]), the agency concerned received criticism for a press photo showing [https://www.businessinsider.com/hawaii-emergency-agency-password-discovered-in-photo-sparks-security-criticism-2018-1?r=US&IR=T a password written on a sticky note] attached to a monitor. |
;A remote attacker can inject arbitrary text into public-facing pages via the comments box. | ;A remote attacker can inject arbitrary text into public-facing pages via the comments box. | ||
:Describes a common feature on news sites or social media sites like Facebook. The possibility for users to "inject" text into the page is by design. This is a humorous reference to the relatively common security vulnerability "[[Wikipedia:Cross-site_scripting|persistent cross-site scripting]]", where input provided by a user, such as through a comment section, can result in dangerous content containing arbitrary HTML or JavaScript code being displayed to other users. | :Describes a common feature on news sites or social media sites like Facebook. The possibility for users to "inject" text into the page is by design. This is a humorous reference to the relatively common security vulnerability "[[Wikipedia:Cross-site_scripting|persistent cross-site scripting]]", where input provided by a user, such as through a comment section, can result in dangerous content containing arbitrary HTML or JavaScript code being displayed to other users. | ||
;MySQL server 5.5.45 secretly runs two parallel databases for people who say "S-Q-L" and "sequel." | ;MySQL server 5.5.45 secretly runs two parallel databases for people who say "S-Q-L" and "sequel." | ||
| − | :Some people pronounce "{{w|SQL}}" like "sequel", after SQL's predecessor "SEQUEL (Structured English Query Language)". The standard for SQL suggests that it should be pronounced as separate letters; however, the author of SQL pronounces it "sequel", so the debate persists (with even more justification than arguments about how to pronounce "GIF"). MySQL is an | + | :Some people pronounce "{{w|SQL}}" like "sequel", after SQL's predecessor "SEQUEL (Structured English Query Language)". The standard for SQL suggests that it should be pronounced as separate letters; however, the author of SQL pronounces it "sequel", so the debate persists (with even <s>more</s> <s>less</s> <s>more</s> <s>less</s> <s>MORE</s> justification than arguments about how to pronounce "GIF"{{Citation needed}}). MySQL is an free relational database management system. The latest generally available version (at the time of writing) is MySQL 5.7. |
;A flaw in some x86 CPUs could allow a root user to de-escalate to normal account privileges. | ;A flaw in some x86 CPUs could allow a root user to de-escalate to normal account privileges. | ||
| − | :{{w|Privilege escalation}} refers to any illegitimate means by which a system user gains greater access privileges than they are supposed to have. The most highly-sought privilege is that of the root user, which allows complete access to an entire system— a ''superuser''. Any flaw that would allow an ordinary user to escalate to superuser status is a critical security threat, as they then have full control of the machine. This is what most | + | :{{w|Privilege escalation}} refers to any illegitimate means by which a system user gains greater access privileges than they are supposed to have. The most highly-sought privilege is that of the root user, which allows complete access to an entire system— a ''superuser''. Any flaw that would allow an ordinary user to escalate to superuser status is a critical security threat, as they then have full control of the machine. This is what most crackers seek to achieve when attacking a device. |
: | : | ||
:This CVE presents the less-threatening reverse situation: allowing a root user to ''de-escalate'' to normal account privileges. In fact, root users can already do this at any time; superuser privileges allow them to take control of any user account, so they can simply switch to an account which has fewer privileges than the root user. | :This CVE presents the less-threatening reverse situation: allowing a root user to ''de-escalate'' to normal account privileges. In fact, root users can already do this at any time; superuser privileges allow them to take control of any user account, so they can simply switch to an account which has fewer privileges than the root user. | ||
;Apple products catch fire when displaying emoji with diacritics. | ;Apple products catch fire when displaying emoji with diacritics. | ||
| − | :This is a reference to a common problem of modern gadgets catching fire (usually related to flaws in lithium-ion batteries), as well as to Apple products crashing when attempting to display certain character sequences. Diacritics are the accents found on letters in some languages ( | + | :This is a reference to a common problem of modern gadgets catching fire (usually related to flaws in lithium-ion batteries), as well as to Apple products crashing when attempting to display certain character sequences. Diacritics are the accents found on letters in some languages, for example the German {{w|Umlaut_(diacritic)|umlaut}} (ü) or the French {{w|cedilla}} (ç). They usually indicate a change to how the letter is pronounced. Diacritics are not normally found on emojis,{{Citation needed}} but since emojis are part of the widely-used {{w|Unicode}} standard which also allows for combining diacritics, it is in fact possible to combine the two to create a diacritical emoji. 🔥̃ is such an example. |
| + | :"Emoji diacritics" may also refer to invisible characters that are used to change the gender or skin color of emoji characters. | ||
;An oversight in the rules allows a dog to join a basketball team. | ;An oversight in the rules allows a dog to join a basketball team. | ||
| − | :This probably refers to the movie {{w|Air Bud}}, about a dog playing basketball. This has been a common theme in xkcd comics: see [[115: Meerkat]], [[1439: Rack Unit]], [[1819: Sweet 16]], [[1552: Rulebook]]. | + | :This probably refers to the movie ''{{w|Air Bud}}'', about a dog playing basketball. This has been a common theme in xkcd comics: see [[115: Meerkat]], [[1439: Rack Unit]], [[1819: Sweet 16]], [[1552: Rulebook]]. |
:In 2017, it was discovered that an oversight in the constitution of the state of Kansas may [http://www.kansascity.com/news/politics-government/article175956836.html permit a dog to be governor]. Shortly before this comic published, the Secretary of State's office ruled that [http://dfw.cbslocal.com/2018/02/13/dog-kansas-governor/ it could not]. | :In 2017, it was discovered that an oversight in the constitution of the state of Kansas may [http://www.kansascity.com/news/politics-government/article175956836.html permit a dog to be governor]. Shortly before this comic published, the Secretary of State's office ruled that [http://dfw.cbslocal.com/2018/02/13/dog-kansas-governor/ it could not]. | ||
;Haskell isn't side-effect-free after all; the effects are all just concentrated in this one computer in Missouri that no one's checked on in a while. | ;Haskell isn't side-effect-free after all; the effects are all just concentrated in this one computer in Missouri that no one's checked on in a while. | ||
| Line 40: | Line 41: | ||
:[[wikipedia:Hypervisor|"Hypervisors"]] are a tool for computer virtualization. Virtualization is implemented via various combinations of hardware and/or software, which requires a computer to completely simulate another computer, with its own unique hardware and software, and to varying degrees as to whether or not the virtualization is aware of or can determine whether it is being virtualized. Many IT professionals and businesses rely heavily on various forms of virtualization, but most of the individual employees would be hard-pressed to explain how it works. Programs running on other virtual computers, or on the real computer, may be able to access information on a virtual computer in ways which would not be possible with a single real computer. Consequently, understanding how the hypervisor works is important to assessing the security of a virtual server. Meltdown and Spectre are related to this. | :[[wikipedia:Hypervisor|"Hypervisors"]] are a tool for computer virtualization. Virtualization is implemented via various combinations of hardware and/or software, which requires a computer to completely simulate another computer, with its own unique hardware and software, and to varying degrees as to whether or not the virtualization is aware of or can determine whether it is being virtualized. Many IT professionals and businesses rely heavily on various forms of virtualization, but most of the individual employees would be hard-pressed to explain how it works. Programs running on other virtual computers, or on the real computer, may be able to access information on a virtual computer in ways which would not be possible with a single real computer. Consequently, understanding how the hypervisor works is important to assessing the security of a virtual server. Meltdown and Spectre are related to this. | ||
;Critical: Under Linux 3.14.8 on System/390 in a UTC+14 time zone, a local user could potentially use a buffer overflow to change another user's default system clock from 12-hour to 24-hour. | ;Critical: Under Linux 3.14.8 on System/390 in a UTC+14 time zone, a local user could potentially use a buffer overflow to change another user's default system clock from 12-hour to 24-hour. | ||
| − | :This joke is about arcane systems that are running Linux in exceedingly rare situations, meaning that reproducing errors would be incredibly difficult or inconvenient, and would only affect a very tiny user base (if any at all). {{w|IBM System/390 ES/9000 Enterprise Systems Architecture ESA family|System/390}} is an IBM mainframe introduced almost 30 years before this comic, which has a version of Linux. UTC+14 is a time zone used only on some islands in the Pacific Ocean (Primarily [[Wikipedia:Line_Islands|the Line Islands]]) and is also the earliest time zone on | + | :This joke is about arcane systems that are running Linux in exceedingly rare situations, meaning that reproducing errors would be incredibly difficult or inconvenient, and would only affect a very tiny user base (if any at all). {{w|IBM System/390 ES/9000 Enterprise Systems Architecture ESA family|System/390}} is an IBM mainframe introduced almost 30 years before this comic, which has a version of Linux. UTC+14 is a time zone used only on some islands in the Pacific Ocean (Primarily [[Wikipedia:Line_Islands|the Line Islands]]) and is also the earliest time zone on Earth. Even if all of these absurd conditions were met, the resulting vulnerability would still be relatively benign: simply changing a user's preferred clock display format. Other xkcd comics make references to such obscure computer-time issues relating to time zones and time conversions, and how many programmers find these issues frustrating or even traumatizing. |
;x86 has way too many instructions. | ;x86 has way too many instructions. | ||
| − | :The x86 architecture (used in many Intel and AMD processors) is very complicated. Processors typically implement such a complex architecture using programs (microcode) run on a set of hidden, proprietary processors. The details of these hidden machines and errors in the microcode can result in security vulnerabilities, such as Meltdown, where the physical machine does not match the conceptual machine. | + | :The x86 architecture (used in many Intel and AMD processors) is very complicated.{{Citation needed}} Processors typically implement such a complex architecture using programs (microcode) run on a set of hidden, proprietary processors. The details of these hidden machines and errors in the microcode can result in security vulnerabilities, such as Meltdown, where the physical machine does not match the conceptual machine. |
: | : | ||
| − | :A more complicated instruction set is more complex to implement.{{Citation needed}} The x86 architecture is considered "CISC" (a "{{w|Complex instruction set computer}}"), having many instructions originally provided to make programming by a human simpler; other examples include the 68000 series used in the first {{w|Apple Macintosh}}. In the 1980s, this design philosophy was countered by the "RISC" ("{{w|Reduced instruction set computer}}") design movement - based on the observation that computer programs were increasingly generated by compilers (which only used a few instructions) rather than directly by people, and that the chip area dedicated to extra instructions could be better dedicated to, for example, cache. Examples of RISC style designs include {{w|SPARC}}, {{w|MIPS}}, {{w|PowerPC}} (used by Apple in later Macintoshes) and the {{w|ARM architecture|ARM}} chips common in mobile phones. Historically, there was considerable discussion about the merits of each approach. At one time the Mac and Windows PC were on different sides; owners of other competing systems such as the Archimedes and Amiga had similar arguments on usenet in the early 1990s. This "issue" may be posted by someone who still recalls these debates. Technically, the extra instructions do slightly complicate the task of validating correct chip | + | :A more complicated instruction set is more complex to implement.{{Citation needed}} The x86 architecture is considered "CISC" (a "{{w|Complex instruction set computer}}"), having many instructions originally provided to make programming by a human simpler; other examples include the 68000 series used in the first {{w|Apple Macintosh}}. In the 1980s, this design philosophy was countered by the "RISC" ("{{w|Reduced instruction set computer}}") design movement - based on the observation that computer programs were increasingly generated by compilers (which only used a few instructions) rather than directly by people, and that the chip area dedicated to extra instructions could be better dedicated to, for example, cache. Examples of RISC style designs include {{w|SPARC}}, {{w|MIPS}}, {{w|PowerPC}} (used by Apple in later Macintoshes) and the {{w|ARM architecture|ARM}} chips common in mobile phones. Historically, there was considerable discussion about the merits of each approach. At one time the Mac and Windows PC were on different sides; owners of other competing systems such as the Archimedes and Amiga had similar arguments on usenet in the early 1990s. This "issue" may be posted by someone who still recalls these debates. Technically, the extra instructions do slightly complicate the task of validating correct chip behavior and complicate the tool chains that manage software, which could be seen as a minor security risk. However, the 64-bit architecture introduced by {{w|AMD}}, and since adopted by {{w|Intel}}, does rationalize things somewhat, and all recent x86 chips break down instructions into RISC-like micro-operations, so the complication from a hardware perspective is localized. Recent security issues, such as the speculative cache load issue in Meltdown and Spectre, depend more on details of implementation, rather than instruction set, and have been exhibited both by x86 (CISC) and ARM (RISC) processors. |
;NumPy 1.8.0 can factor primes in ''O''(log ''n'') time and must be quietly deprecated before anyone notices. | ;NumPy 1.8.0 can factor primes in ''O''(log ''n'') time and must be quietly deprecated before anyone notices. | ||
:Fantastically, this would be an unimaginable software threat, not to be confused with the even speedier, but future-bound, threat in hardware via {{w|Quantum computing}}. | :Fantastically, this would be an unimaginable software threat, not to be confused with the even speedier, but future-bound, threat in hardware via {{w|Quantum computing}}. | ||
| Line 51: | Line 52: | ||
:Another joke on the first CVE and [[wikipedia:I before E except after C|a common English writing rule of thumb]], which fails almost as often as it succeeds. Possibly a jab at Apple's image, portraying their software as unable to handle improper grammar or spelling. | :Another joke on the first CVE and [[wikipedia:I before E except after C|a common English writing rule of thumb]], which fails almost as often as it succeeds. Possibly a jab at Apple's image, portraying their software as unable to handle improper grammar or spelling. | ||
;Skylake x86 chips can be pried from their sockets using certain flathead screwdrivers. | ;Skylake x86 chips can be pried from their sockets using certain flathead screwdrivers. | ||
| − | :Skylake x86 chips are a line of microprocessors made by Intel. Some processors are soldered directly to a system board or daughter board, while others are attached to boards that plug into the system board by means of a socket (pins or connectors that make physical contact with receptacles or connectors on a system board). Some sockets, especially older ones, require force to insert or remove, and often require the use of a flat blade screwdriver or a specialized tool, but most modern ones use ZIF (Zero Insertion Force) techniques, often involving a lever or similar to tighten or loosen the friction/tightness of the contacts. No screwdriver is needed in this case. However, any | + | :Skylake x86 chips are a line of microprocessors made by Intel. Some processors are soldered directly to a system board or daughter board, while others are attached to boards that plug into the system board by means of a socket (pins or connectors that make physical contact with receptacles or connectors on a system board). Some sockets, especially older ones, require force to insert or remove, and often require the use of a flat blade screwdriver or a specialized tool, but most modern ones use ZIF (Zero Insertion Force) techniques, often involving a lever or similar to tighten or loosen the friction/tightness of the contacts. No screwdriver is needed in this case. However, ''any'' processor can be forcefully removed from its socket with a screwdriver.{{Citation needed}} |
;Apparently Linus Torvalds can be bribed pretty easily. | ;Apparently Linus Torvalds can be bribed pretty easily. | ||
:{{w|Linus Torvalds}} is the {{w|benevolent dictator for life}} of the Linux kernel codebase. Normally it is hard to make changes because he has the last word, and because the kernel is replicated in all Linux installations. Linus made the news in January 2018 when, having looked at one of Intel's proposed fixes for the Spectre and Meltdown vulnerabilities, he declared "[https://techcrunch.com/2018/01/22/linus-torvalds-declares-intel-fix-for-meltdown-spectre-complete-and-utter-garbage/ the patches are COMPLETE AND UTTER GARBAGE]". Presumably, it may be found that he may be successfully bribed to be less blunt and/or less critical of vulnerability fixes that are complete and/or utter garbage. If this were the case, this would be a severe critical vulnerability to all Linux servers and machines. | :{{w|Linus Torvalds}} is the {{w|benevolent dictator for life}} of the Linux kernel codebase. Normally it is hard to make changes because he has the last word, and because the kernel is replicated in all Linux installations. Linus made the news in January 2018 when, having looked at one of Intel's proposed fixes for the Spectre and Meltdown vulnerabilities, he declared "[https://techcrunch.com/2018/01/22/linus-torvalds-declares-intel-fix-for-meltdown-spectre-complete-and-utter-garbage/ the patches are COMPLETE AND UTTER GARBAGE]". Presumably, it may be found that he may be successfully bribed to be less blunt and/or less critical of vulnerability fixes that are complete and/or utter garbage. If this were the case, this would be a severe critical vulnerability to all Linux servers and machines. | ||
| Line 60: | Line 61: | ||
:Other than by some {{w|metadata}}, either internal to the image file, or embedded along with it, as in a web page, or a PDF or other container file, this "bug" would require the device to {{w|Hard AI|figure out}} specifically what the photo contains image-wise (something that's REALLY HARD for computers to do reliably), but would also require OCR (optical character recognition) code to convert the text superimposed on the photo into executable code. In other words, it's hard to believe in 2018 that such a bug could exist. Maybe in the future when such things are more routine...? As an example, OCR used to be hard to do reliably, but now it's a lot more routine and built into a lot of devices. | :Other than by some {{w|metadata}}, either internal to the image file, or embedded along with it, as in a web page, or a PDF or other container file, this "bug" would require the device to {{w|Hard AI|figure out}} specifically what the photo contains image-wise (something that's REALLY HARD for computers to do reliably), but would also require OCR (optical character recognition) code to convert the text superimposed on the photo into executable code. In other words, it's hard to believe in 2018 that such a bug could exist. Maybe in the future when such things are more routine...? As an example, OCR used to be hard to do reliably, but now it's a lot more routine and built into a lot of devices. | ||
;Under rare circumstances, a flaw in some versions of Windows could allow Flash to be installed. | ;Under rare circumstances, a flaw in some versions of Windows could allow Flash to be installed. | ||
| − | :Flash has been an integral browser plugin for decades, but has fallen out of favor in the 2010s, and eventually discontinued because of its notoriously abysmal security record. All security experts advise against installing it. Preventing installation of Flash would make systems more secure, but most versions of Windows do not prevent Flash installation. The joke here relates to the difficulty of keeping Flash up to date, or even installed properly to begin with. A common user experience, which is the subject of numerous jokes and memes, is the constant nagging notification to install or update Flash in order for web pages to display properly. Many IT professionals will bemoan the trouble they have experienced in the workplace due to these notifications and problems related to them. | + | :Adobe Flash has been an integral browser plugin for decades, but has fallen out of favor in the 2010s, and eventually discontinued because of its notoriously abysmal security record. All security experts advise against installing it. Preventing installation of Flash would make systems more secure, but most versions of Windows do not prevent Flash installation (provided, as of 2021, the user still has a copy of the files with which to do so). The joke here relates to the difficulty of keeping Flash up to date, or even installed properly to begin with. A common user experience, which is the subject of numerous jokes and memes, is the constant nagging notification to install or update Flash in order for web pages to display properly. Many IT professionals will bemoan the trouble they have experienced in the workplace due to these notifications and problems related to them. |
| + | :In late 2020, Microsoft [https://support.microsoft.com/en-us/help/4577586/update-for-removal-of-adobe-flash-player released an optional Windows update] that removes Flash and prevents users from installing it again. | ||
;Turns out the cloud is just other people's computers. | ;Turns out the cloud is just other people's computers. | ||
| − | : | + | :Cloud computing is a system of networked computers wherein the client user's computer can offload some of its work load and storage to the other computers — known as "the cloud." Many businesses offer their networks for consumer use, and can be marketed as "{{w|Platform as a Service}}" ("PaaS") or simply "cloud service." As with any product companies are always tempted to overhype what they offer, promising cloud computing to be more powerful and wondrous than it actually is. Thus, protestors try to remind people what cloud services really are by referring to "the cloud" as "other people's computers." This is, at its core, entirely accurate, taking away the business jargon and simplifying the situation in such a way that it might cast doubt on the security, reliability, and general effectiveness of using "cloud" solutions. In [[908: The Cloud]], it turns out that [[Black Hat]] is the "other people" whose computer ''is'' the Cloud. |
;A flaw in Mitre's CVE database allows arbitrary code insertion.[[779|[~~CLICK HERE FOR CHEAP VIAGRA~~]]] | ;A flaw in Mitre's CVE database allows arbitrary code insertion.[[779|[~~CLICK HERE FOR CHEAP VIAGRA~~]]] | ||
| − | :Mitre's CVE database is where all {{w|Common Vulnerabilities and Exposures|CVEs}} are stored. This log message forms the punchline of the comic, as it implies that all of the exaggerated error messages above might have been inserted by | + | :Mitre's CVE database is where all {{w|Common Vulnerabilities and Exposures|CVEs}} are stored. This log message forms the punchline of the comic, as it implies that all of the exaggerated error messages above might have been inserted by crackers exploiting the vulnerability. To pour salt in the wound, they then included in a typical spam link purporting to offer inexpensive {{w|Viagra|brand-name Sildenafil}}. |
;It turns out Bruce Schneier is just two mischevious kids in a trenchcoat. | ;It turns out Bruce Schneier is just two mischevious kids in a trenchcoat. | ||
:Appears in the title text. {{w|Bruce Schneier}} is security researcher and blogger. The "two kids in a trenchcoat" is a reference to the {{tvtropes|TotemPoleTrench|Totem Pole Trench}} trope. Shortly before this comic was posted, a [https://rare.us/rare-humor/two-kids-dressed-as-a-tall-man-to-get-into-black-panther-is-caught-on-video story went viral] in which two kids were photographed attempting this for real to get into a screening of ''Black Panther''. | :Appears in the title text. {{w|Bruce Schneier}} is security researcher and blogger. The "two kids in a trenchcoat" is a reference to the {{tvtropes|TotemPoleTrench|Totem Pole Trench}} trope. Shortly before this comic was posted, a [https://rare.us/rare-humor/two-kids-dressed-as-a-tall-man-to-get-into-black-panther-is-caught-on-video story went viral] in which two kids were photographed attempting this for real to get into a screening of ''Black Panther''. | ||
| Line 96: | Line 98: | ||
==Trivia== | ==Trivia== | ||
| − | Randall has previously referenced diacritics in [[1647: Diacritics]]. | + | *The word "exploit" in the second line is apparently misspelled. |
| + | * Randall has previously referenced diacritics in [[1647: Diacritics]]. | ||
| − | Bruce Schneier was previously mentioned in the title texts of [[748: Worst-Case Scenario]] and [[1039: RuBisCO]]. | + | * Bruce Schneier was previously mentioned in the title texts of [[748: Worst-Case Scenario]] and [[1039: RuBisCO]]. |
{{comic discussion}} | {{comic discussion}} | ||
[[Category:Comics with color]] | [[Category:Comics with color]] | ||
| + | [[Category:Comics with lowercase text]] | ||
[[Category:Charts]] | [[Category:Charts]] | ||
| + | [[Category:Language]] | ||
[[Category:Programming]] | [[Category:Programming]] | ||
[[Category:Computers]] | [[Category:Computers]] | ||
| + | [[Category:iOS]] | ||
Latest revision as of 09:19, 26 October 2024
| 2018 CVE List |
 Title text: CVE-2018-?????: It turns out Bruce Schneier is just two mischevious kids in a trenchcoat. |
Explanation[edit]
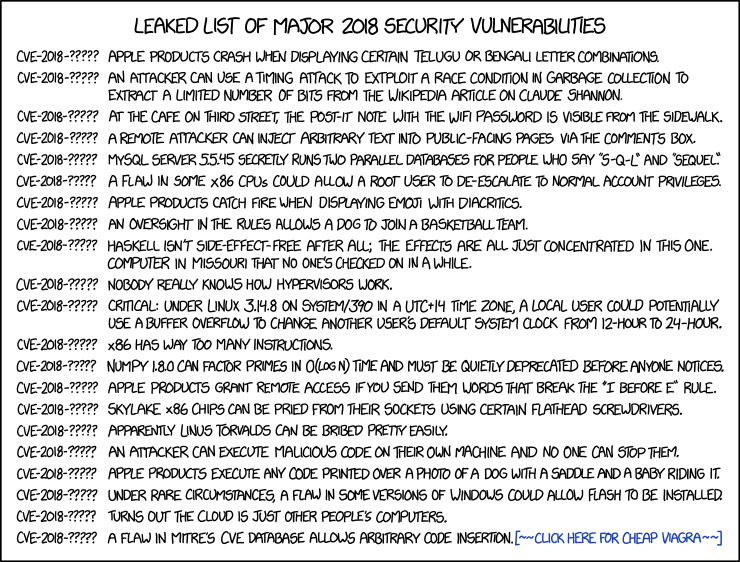
CVE (Common Vulnerabilities and Exposures) is a standardized format for assigning an identity to a cybersecurity vulnerability (similar to the way that astronomical bodies are assigned unique identifiers by committees). Giving vulnerabilities a unique identifier makes them easier to talk about and helps in keeping track of the progress made toward resolving them. The typical format of a CVE identifier is CVE-[YEAR]-[NUMBER]. For example, the CVE identifier for 2017's widespread Meltdown vulnerability is CVE-2017-5754. CVEs also contain a short description of the issue.
In this comic (released in February 2018), Randall presents a number of spurious predicted CVEs for later in 2018. Each CVE identifier is given as "CVE-2018-?????", reflecting the fact that they have not yet happened so we don't know exactly what their CVE identifier will be.
Following are short descriptions of all the vulnerabilities mentioned in the comic.
- Apple products crash when displaying certain Telugu or Bengali letter combinations.
- This refers to a real vulnerability in iOS and MacOS publicized a few days before the comic was released, as well as past similar iOS vulnerabilities.
- An attacker can use a timing attack to extploit [sic] a race condition in garbage collection to extract a limited number of bits from the Wikipedia article on Claude Shannon.
- The reference to using a Timing Attack to exploit a race condition in garbage collection refers to Meltdown and Spectre CPU flaws that can be exploited in a cloud server like the ones in Wikipedia. Claude Shannon was an early and highly influential information scientist whose work underlies compression, encryption, security, and the theory behind how information is encoded into binary digits.
- This is not a security problem, since Wikipedia articles are public. However, since Shannon formulated how the amount of unique or actual information some entity contains is proportional to the number of bits required to encode it, retrieving only a few bits casts a dark perspective upon the significance of the Shannon article's content.
- At the cafe on Third Street, the Post-it note with the WiFi password is visible from the sidewalk.
- Cafés often offer free access to WiFi as a service to patrons, as a business strategy to encourage said patrons to remain in the building and buy more coffee. Some use a password, so that only patrons can use the WiFi, and may display the password on signage inside. Since anybody could go into the cafe to read the post-it, and then use the network from nearby, the ability to read it from outside is, at most, a trivial problem. For systems that are supposed to be secure, writing passwords in a visible place is a major security flaw. For instance, following the 2018 Hawaii false missile alert (see Hawaii), the agency concerned received criticism for a press photo showing a password written on a sticky note attached to a monitor.
- A remote attacker can inject arbitrary text into public-facing pages via the comments box.
- Describes a common feature on news sites or social media sites like Facebook. The possibility for users to "inject" text into the page is by design. This is a humorous reference to the relatively common security vulnerability "persistent cross-site scripting", where input provided by a user, such as through a comment section, can result in dangerous content containing arbitrary HTML or JavaScript code being displayed to other users.
- MySQL server 5.5.45 secretly runs two parallel databases for people who say "S-Q-L" and "sequel."
- Some people pronounce "SQL" like "sequel", after SQL's predecessor "SEQUEL (Structured English Query Language)". The standard for SQL suggests that it should be pronounced as separate letters; however, the author of SQL pronounces it "sequel", so the debate persists (with even
morelessmorelessMOREjustification than arguments about how to pronounce "GIF"[citation needed]). MySQL is an free relational database management system. The latest generally available version (at the time of writing) is MySQL 5.7. - A flaw in some x86 CPUs could allow a root user to de-escalate to normal account privileges.
- Privilege escalation refers to any illegitimate means by which a system user gains greater access privileges than they are supposed to have. The most highly-sought privilege is that of the root user, which allows complete access to an entire system— a superuser. Any flaw that would allow an ordinary user to escalate to superuser status is a critical security threat, as they then have full control of the machine. This is what most crackers seek to achieve when attacking a device.
- This CVE presents the less-threatening reverse situation: allowing a root user to de-escalate to normal account privileges. In fact, root users can already do this at any time; superuser privileges allow them to take control of any user account, so they can simply switch to an account which has fewer privileges than the root user.
- Apple products catch fire when displaying emoji with diacritics.
- This is a reference to a common problem of modern gadgets catching fire (usually related to flaws in lithium-ion batteries), as well as to Apple products crashing when attempting to display certain character sequences. Diacritics are the accents found on letters in some languages, for example the German umlaut (ü) or the French cedilla (ç). They usually indicate a change to how the letter is pronounced. Diacritics are not normally found on emojis,[citation needed] but since emojis are part of the widely-used Unicode standard which also allows for combining diacritics, it is in fact possible to combine the two to create a diacritical emoji. 🔥̃ is such an example.
- "Emoji diacritics" may also refer to invisible characters that are used to change the gender or skin color of emoji characters.
- An oversight in the rules allows a dog to join a basketball team.
- This probably refers to the movie Air Bud, about a dog playing basketball. This has been a common theme in xkcd comics: see 115: Meerkat, 1439: Rack Unit, 1819: Sweet 16, 1552: Rulebook.
- In 2017, it was discovered that an oversight in the constitution of the state of Kansas may permit a dog to be governor. Shortly before this comic published, the Secretary of State's office ruled that it could not.
- Haskell isn't side-effect-free after all; the effects are all just concentrated in this one computer in Missouri that no one's checked on in a while.
- Haskell is a functional programming language. Functional programming is characterized by using functions that don't have side effects because they can not change things accessible in other parts of the program, as in 1312: Haskell. The joke here is discovering that it does indeed have side-effects, manifested via external alteration, not violating the internal alteration paradigm. It may also be a reference to "The Ones Who Walk Away From Omelas," a short story by Ursula Le Guin in which a utopian city concentrates all its misery into one child who is locked away in a basement.
- Nobody really knows how hypervisors work.
- "Hypervisors" are a tool for computer virtualization. Virtualization is implemented via various combinations of hardware and/or software, which requires a computer to completely simulate another computer, with its own unique hardware and software, and to varying degrees as to whether or not the virtualization is aware of or can determine whether it is being virtualized. Many IT professionals and businesses rely heavily on various forms of virtualization, but most of the individual employees would be hard-pressed to explain how it works. Programs running on other virtual computers, or on the real computer, may be able to access information on a virtual computer in ways which would not be possible with a single real computer. Consequently, understanding how the hypervisor works is important to assessing the security of a virtual server. Meltdown and Spectre are related to this.
- Critical: Under Linux 3.14.8 on System/390 in a UTC+14 time zone, a local user could potentially use a buffer overflow to change another user's default system clock from 12-hour to 24-hour.
- This joke is about arcane systems that are running Linux in exceedingly rare situations, meaning that reproducing errors would be incredibly difficult or inconvenient, and would only affect a very tiny user base (if any at all). System/390 is an IBM mainframe introduced almost 30 years before this comic, which has a version of Linux. UTC+14 is a time zone used only on some islands in the Pacific Ocean (Primarily the Line Islands) and is also the earliest time zone on Earth. Even if all of these absurd conditions were met, the resulting vulnerability would still be relatively benign: simply changing a user's preferred clock display format. Other xkcd comics make references to such obscure computer-time issues relating to time zones and time conversions, and how many programmers find these issues frustrating or even traumatizing.
- x86 has way too many instructions.
- The x86 architecture (used in many Intel and AMD processors) is very complicated.[citation needed] Processors typically implement such a complex architecture using programs (microcode) run on a set of hidden, proprietary processors. The details of these hidden machines and errors in the microcode can result in security vulnerabilities, such as Meltdown, where the physical machine does not match the conceptual machine.
- A more complicated instruction set is more complex to implement.[citation needed] The x86 architecture is considered "CISC" (a "Complex instruction set computer"), having many instructions originally provided to make programming by a human simpler; other examples include the 68000 series used in the first Apple Macintosh. In the 1980s, this design philosophy was countered by the "RISC" ("Reduced instruction set computer") design movement - based on the observation that computer programs were increasingly generated by compilers (which only used a few instructions) rather than directly by people, and that the chip area dedicated to extra instructions could be better dedicated to, for example, cache. Examples of RISC style designs include SPARC, MIPS, PowerPC (used by Apple in later Macintoshes) and the ARM chips common in mobile phones. Historically, there was considerable discussion about the merits of each approach. At one time the Mac and Windows PC were on different sides; owners of other competing systems such as the Archimedes and Amiga had similar arguments on usenet in the early 1990s. This "issue" may be posted by someone who still recalls these debates. Technically, the extra instructions do slightly complicate the task of validating correct chip behavior and complicate the tool chains that manage software, which could be seen as a minor security risk. However, the 64-bit architecture introduced by AMD, and since adopted by Intel, does rationalize things somewhat, and all recent x86 chips break down instructions into RISC-like micro-operations, so the complication from a hardware perspective is localized. Recent security issues, such as the speculative cache load issue in Meltdown and Spectre, depend more on details of implementation, rather than instruction set, and have been exhibited both by x86 (CISC) and ARM (RISC) processors.
- NumPy 1.8.0 can factor primes in O(log n) time and must be quietly deprecated before anyone notices.
- Fantastically, this would be an unimaginable software threat, not to be confused with the even speedier, but future-bound, threat in hardware via Quantum computing.
- NumPy is the fundamental package for scientific computing with the programming language Python. O(log n) is Big O notation meaning that the time it takes for a computer algorithm to run is in the order of log n, for an input of size n. O(log n) is very fast and is more usual for a search algorithm. Prime factorization currently is O(2nn)). If something can find the prime factors of a number this quickly, especially a semiprime with two large factors, it will enable attacks to break many crypto functions used in internet security. However, prime numbers have only a single factor, and "factoring primes" quickly is a simpler problem, that of proving that a number is in fact a prime.
- Apple products grant remote access if you send them words that break the "I before E" rule.
- Another joke on the first CVE and a common English writing rule of thumb, which fails almost as often as it succeeds. Possibly a jab at Apple's image, portraying their software as unable to handle improper grammar or spelling.
- Skylake x86 chips can be pried from their sockets using certain flathead screwdrivers.
- Skylake x86 chips are a line of microprocessors made by Intel. Some processors are soldered directly to a system board or daughter board, while others are attached to boards that plug into the system board by means of a socket (pins or connectors that make physical contact with receptacles or connectors on a system board). Some sockets, especially older ones, require force to insert or remove, and often require the use of a flat blade screwdriver or a specialized tool, but most modern ones use ZIF (Zero Insertion Force) techniques, often involving a lever or similar to tighten or loosen the friction/tightness of the contacts. No screwdriver is needed in this case. However, any processor can be forcefully removed from its socket with a screwdriver.[citation needed]
- Apparently Linus Torvalds can be bribed pretty easily.
- Linus Torvalds is the benevolent dictator for life of the Linux kernel codebase. Normally it is hard to make changes because he has the last word, and because the kernel is replicated in all Linux installations. Linus made the news in January 2018 when, having looked at one of Intel's proposed fixes for the Spectre and Meltdown vulnerabilities, he declared "the patches are COMPLETE AND UTTER GARBAGE". Presumably, it may be found that he may be successfully bribed to be less blunt and/or less critical of vulnerability fixes that are complete and/or utter garbage. If this were the case, this would be a severe critical vulnerability to all Linux servers and machines.
- An attacker can execute malicious code on their own machine and no one can stop them.
- The point of an attack is to make someone else's machine perform actions against the owner's will. Anyone can make their own machine execute any code if they have root access and the necessary tools, but this would usually not be described as an attack, except in the case of a locked-down appliance, such as a video game console, a John Deere tractor, or pay TV decoder.
- Apple products execute any code printed over a photo of a dog with a saddle and a baby riding it.
- This could refer to a CVE vulnerability of JPG files where JavaScript embedded within the image file is executed by some application. In this case, though, the code is visible on the image instead of invisibly encoded within the image file. The code is also only executed if the image contains a photo of a baby in a saddle riding a dog. It's unclear whether the photo would be a digital photo, a printed photo (i.e. as taken using a digital camera), or maybe both.
- Other than by some metadata, either internal to the image file, or embedded along with it, as in a web page, or a PDF or other container file, this "bug" would require the device to figure out specifically what the photo contains image-wise (something that's REALLY HARD for computers to do reliably), but would also require OCR (optical character recognition) code to convert the text superimposed on the photo into executable code. In other words, it's hard to believe in 2018 that such a bug could exist. Maybe in the future when such things are more routine...? As an example, OCR used to be hard to do reliably, but now it's a lot more routine and built into a lot of devices.
- Under rare circumstances, a flaw in some versions of Windows could allow Flash to be installed.
- Adobe Flash has been an integral browser plugin for decades, but has fallen out of favor in the 2010s, and eventually discontinued because of its notoriously abysmal security record. All security experts advise against installing it. Preventing installation of Flash would make systems more secure, but most versions of Windows do not prevent Flash installation (provided, as of 2021, the user still has a copy of the files with which to do so). The joke here relates to the difficulty of keeping Flash up to date, or even installed properly to begin with. A common user experience, which is the subject of numerous jokes and memes, is the constant nagging notification to install or update Flash in order for web pages to display properly. Many IT professionals will bemoan the trouble they have experienced in the workplace due to these notifications and problems related to them.
- In late 2020, Microsoft released an optional Windows update that removes Flash and prevents users from installing it again.
- Turns out the cloud is just other people's computers.
- Cloud computing is a system of networked computers wherein the client user's computer can offload some of its work load and storage to the other computers — known as "the cloud." Many businesses offer their networks for consumer use, and can be marketed as "Platform as a Service" ("PaaS") or simply "cloud service." As with any product companies are always tempted to overhype what they offer, promising cloud computing to be more powerful and wondrous than it actually is. Thus, protestors try to remind people what cloud services really are by referring to "the cloud" as "other people's computers." This is, at its core, entirely accurate, taking away the business jargon and simplifying the situation in such a way that it might cast doubt on the security, reliability, and general effectiveness of using "cloud" solutions. In 908: The Cloud, it turns out that Black Hat is the "other people" whose computer is the Cloud.
- A flaw in Mitre's CVE database allows arbitrary code insertion.[~~CLICK HERE FOR CHEAP VIAGRA~~]
- Mitre's CVE database is where all CVEs are stored. This log message forms the punchline of the comic, as it implies that all of the exaggerated error messages above might have been inserted by crackers exploiting the vulnerability. To pour salt in the wound, they then included in a typical spam link purporting to offer inexpensive brand-name Sildenafil.
- It turns out Bruce Schneier is just two mischevious kids in a trenchcoat.
- Appears in the title text. Bruce Schneier is security researcher and blogger. The "two kids in a trenchcoat" is a reference to the Totem Pole Trench trope. Shortly before this comic was posted, a story went viral in which two kids were photographed attempting this for real to get into a screening of Black Panther.
Transcript[edit]
- [A heading is centered above a list of 21 vulnerabilities]
- Leaked list of major 2018 security vulnerabilities
- CVE-2018-????? Apple products crash when displaying certain Telugu or Bengali letter combinations.
- CVE-2018-????? An attacker can use a timing attack to extploit a race condition in garbage collection to extract a limited number of bits from the Wikipedia article on Claude Shannon.
- CVE-2018-????? At the cafe on Third Street, the Post-it note with the WiFi password is visible from the sidewalk.
- CVE-2018-????? A remote attacker can inject arbitrary text into public-facing pages via the comments box.
- CVE-2018-????? MySQL server 5.5.45 secretly runs two parallel databases for people who say "S-Q-L" and "sequel."
- CVE-2018-????? A flaw in some x86 CPUs could allow a root user to de-escalate to normal account privileges.
- CVE-2018-????? Apple products catch fire when displaying emoji with diacritics.
- CVE-2018-????? An oversight in the rules allows a dog to join a basketball team.
- CVE-2018-????? Haskell isn't side-effect-free after all; the effects are all just concentrated in this one. computer in Missouri that no one's checked on in a while.
- CVE-2018-????? Nobody really knows how hypervisors work.
- CVE-2018-????? Critical: Under Linux 3.14.8 on System/390 in a UTC+14 time zone, a local user could potentially use a buffer overflow to change another user's default system clock from 12-hour to 24-hour.
- CVE-2018-????? x86 has way too many instructions.
- CVE-2018-????? NumPy 1.8.0 can factor primes in O(log n) time and must be quietly deprecated before anyone notices.
- CVE-2018-????? Apple products grant remote access if you send them words that break the "I before E" rule.
- CVE-2018-????? Skylake x86 chips can be pried from their sockets using certain flathead screwdrivers.
- CVE-2018-????? Apparently Linus Torvalds can be bribed pretty easily.
- CVE-2018-????? An attacker can execute malicious code on their own machine and no one can stop them.
- CVE-2018-????? Apple products execute any code printed over a photo of a dog with a saddle and a baby riding it.
- CVE-2018-????? Under rare circumstances, a flaw in some versions of Windows could allow Flash to be installed.
- CVE-2018-????? Turns out the cloud is just other people's computers.
- CVE-2018-????? A flaw in Mitre's CVE database allows arbitrary code insertion.[~~Click here for cheap viagra~~]
Trivia[edit]
- The word "exploit" in the second line is apparently misspelled.
- Randall has previously referenced diacritics in 1647: Diacritics.
- Bruce Schneier was previously mentioned in the title texts of 748: Worst-Case Scenario and 1039: RuBisCO.
Discussion
First post!!!!!!!!!!!!!!!!!!!!!!!!!!! Anyway, the explanation looks like a train wreck, and I'm not sure if a rearranging it into a table or just adding bullet points to everything is better. I'm guessing that a table would be better, but I don't know how I can rearrange it. Can somebody help? Herobrine (talk) 06:35, 19 February 2018 (UTC)
- Thank you so much for using a list instead of a table! I read this on an Android phone, and tables on this site are hard to read. The first column comes out with really small text, and since the cell vertical alignment is not 'top' I have to scroll down to find what the row is about, then scroll back up to try to find the rest of the row. Your list format is far superior IMO 162.158.38.58 11:49, 24 February 2020 (UTC)
- Added a table layout to the sandbox. Might be of some use to another editor. 162.158.74.45 07:32, 19 February 2018 (UTC)
- Edit: Looks like it's been adapted in; I've cleared the sandbox for future use. 162.158.74.45 11:53, 19 February 2018 (UTC)
- Thanks, I think a table is a good way to go. I'm adding it to the article as a place to start. Rather than format the original explanation into the table, I'm leaving the cells blank. The original poorly formatted text can be a starting point, but isn't directly adaptable. --Quantum7 (talk) 09:55, 19 February 2018 (UTC)
Never ever have I heard anyone pronounce SQL as "sequel" - Is that a reqional dialect? 162.158.93.15 07:41, 19 February 2018 (UTC)
- I heard it's common among MS-SQL users.--162.158.91.137 08:02, 19 February 2018 (UTC)
- Oh BTW, look at our IPs. Are you an easybell customer? :-) --162.158.91.137 08:09, 19 February 2018 (UTC)
- I somewhat doubt we are using easybell, from the looks of it it's not suited for the size of our company. But I can neither verify nor deny that claim as I am not responsible for the WAN connection at our company. 162.158.93.9 15:09, 19 February 2018 (UTC)
- Oh BTW, look at our IPs. Are you an easybell customer? :-) --162.158.91.137 08:09, 19 February 2018 (UTC)
- Some people pronounce it that way, yes. Don't know if it is "common among MS-SQL users", though. The only person I encountered saying "sequel" never used MS-SQL. LordHorst (talk) 09:54, 19 February 2018 (UTC)
- Not sure if it's regional or not. I personally say "sequel" and I'd say anecdotally that it's about 50/50 among people that I've worked with. I went to school and work in the Midwest US. 108.162.216.94 15:40, 19 February 2018 (UTC)
- I've also seen references to Oracle users saying "sequel" rather than S-Q-L. That would make sense as it's the DB I'm primarily working with. http://patorjk.com/blog/2012/01/26/pronouncing-sql-s-q-l-or-sequel/ 108.162.216.94 15:43, 19 February 2018 (UTC)
- Monty (BDFL for MySQL) always pronounces it as "My ess cue ell". RandalSchwartz (talk) 18:22, 19 February 2018 (UTC)
- I've always said 'sequel' but then 'my ess kyoo ell'. Which makes no sense really. 162.158.155.26 09:40, 20 February 2018 (UTC)
- When I was in college a couple decades back I have memory of the professor that taught SQL saying that pronouncing it "sequel" had been registered as a trademark of Micosoft. He instructed us to avoid that pronunciation whenever possible because of this. I have not fact-checked this statement. Odysseus654 (talk) 22:00, 19 February 2018 (UTC)
- I like to pronounce it "squeel" because that's equally correct phonetically & it never fails to raise eyebrows. ProphetZarquon (talk) 00:33, 20 February 2018 (UTC)
- I hear it occasionally, even myself once in a while. However, I seriously doubt EVERYBODY who does so is referencing the predecessor, pretty sure everybody I've heard say "sequel" does so because SQL looks like it's short for "sequel", thats all. NiceGuy1 (talk) 05:04, 20 February 2018 (UTC)
- Always called it 'Squirrel' myself. Squirrels are more fun, sequels are generally bad, and prequels even worse. --162.158.186.18 08:23, 1 April 2018 (UTC)
I want to take a moment to congratulate the dedication of whomever wrote the original explanation. Second languages are hard, bro. 108.162.215.10 07:48, 19 February 2018 (UTC)
Has someone tried contacting Randall about "extploit"? If not, what would be the best way? Fabian42 (talk) 08:22, 19 February 2018 (UTC)
- Hack his computer to display a message demanding he fix it if he wants his hard drive decrypted.162.158.155.26 09:24, 19 February 2018 (UTC)
- Thanks, will do.
- If anyone is getting this changed to correct silly errors, removing the full stop in “…one. Computer…” would be nice. 141.101.99.197 15:22, 19 February 2018 (UTC)
- Urban Dictionary suggestion: EXTploit - A trojan (usually bearing a harmless looking icon) which takes advantage of the idiotic practice of hiding filename extensions by default within major operating systems. This increases the likelihood that a user will execute the trojan, thinking it is a media file because they cannot see the actual file-extension. ProphetZarquon (talk) 00:33, 20 February 2018 (UTC)
Regarding "Factor a prime": Factoring a prime is easy: The prime itself is the only factor, so it's sufficient to use AKS or whatever to check that. Public-key encryption relies on how hard it is to factor the product of two primes, which is a much harder problem. Maybe this is a typo in the comic? -- Comment Police (talk) (please sign your comments with ~~~~)
- I don't think it is a typo. It's exactly the type of "inside-joke" I would expect from XKCD. :) --162.158.134.214 10:09, 19 February 2018 (UTC)
- AFAIK, there aren't any primality tests known to run in O(log n). For instance, AKS runs in O(log n ^ 7.5). So for numpy to actually achieve factoring as stated would require assuming the input is prime and just returning (1,n). --Quantum7 (talk) 12:45, 19 February 2018 (UTC)
- Doesn't testing for primality (just) require a list of all primes up to sqrt(n)? So the best possible time is sqrt(however fast you can calculate primes up to a number). That time can at most be square (divide every number by every other number below it), so a primality test only needs O(n) time. Or do I understand something wrong? Fabian42 (talk) 13:46, 19 February 2018 (UTC)
- AFAIK, there aren't any primality tests known to run in O(log n). For instance, AKS runs in O(log n ^ 7.5). So for numpy to actually achieve factoring as stated would require assuming the input is prime and just returning (1,n). --Quantum7 (talk) 12:45, 19 February 2018 (UTC)
- On the other hand, consider the following phrases that describe a process using the end result of the process as their direct object: "cook scrambled eggs", "bake a cake", "chop firewood", "encode an MP3", and "factor primes". One would "factor primes" out of the semiprime associated with an RSA key. --Tepples (talk) 15:58, 19 February 2018 (UTC)
- There are a bunch of things going on:
- * NumPy currently has no primality or factoring functions. SymPy does. We assume the hypothetical CVE happened because someone added it.
- * Factoring a prime is a bit nonsensical. We factor into primes or perform a primality test. Perhaps a reference to the humorously mis-spoken Bill Gates quote: "The obvious mathematical breakthrough would be development of an easy way to factor large prime numbers." -Bill Gates, The Road Ahead, pg. 265. We know what he meant (and he likely does too) but it's technically just wrong.
- * The best known factoring methods are sub-exponential, not polynomial as $O(\log n)$ indicates. The current explanation test here is factually wrong (but gets the concept across) -- it isn't $O(2^n)$.
- * Deterministic 64-bit primality testing is $O(\log^2 n)$ using BPSW or deterministic Miller-Rabin. This worse than $O(\log n)$.
- * Heuristic or probabilistic testing for larger inputs is also $O(\log^2 n)$. The best deterministic method for larger inputs is ECPP at $O(\log^4 n)$, which is faster than AKS's $O(\log^6 n)$ in addition to much smaller constants.
- Ignoring or being amused at the "factoring primes" comment, we see the complexity is actually in the correct form (most internet forum contributers mix up "n" vs. "size of n", for example). If it were factoring composites, then $O(log^k n)$ for any constant 'k' would be funny as it says nobody noticed they added a polynomial time factoring algorithm. If it is primality testing then it's funny as-is since this is faster than any known method (basically saying you could do a primality test on any size input with a constant number of multiplies).
- DAJ NT (talk) 19:29, 22 February 2018 (UTC)
Can I edit some spelling errors? There seems to be some spelling errors here and there.Boeing-787lover 10:19, 19 February 2018 (UTC)
I think the explanation of the one about injecting arbitrary text onto a page with the comments box is overthinking the joke. I think it really is just about the fact that you can write whatever you like in a comment. Look, I just hacked this page to display the word "penguin". Jeremyp (talk) 10:26, 19 February 2018 (UTC)
- I think it can generally be agreed, at least among most people above a certain level of computer knowledge, that this doesn't count as hacking. :) "Hacking" is helping yourself to greater access than you're supposed to have, and requires considerable skill and advanced tools to accomplish. THIS "hacking", both adding to the page and as described in the comic, is perfectly allowed and requires no special knowledge. Wherein lies the joke. :) NiceGuy1 (talk) 05:13, 23 February 2018 (UTC)
Since when is Bruce Schneier not real? 162.158.93.75 13:05, 19 February 2018 (UTC)
- He never was - it's a cleverly executed art project. 141.101.99.209 14:20, 19 February 2018 (UTC)
I've added some clarification to the "CRITICAL" item. I know there are several xkcd comics referencing similar problems but I unfortunately don't have the time to look them up, can someone do that and link them appropriately in the table? Domino (talk) 13:11, 19 February 2018 (UTC)domino
- Isn't the joke really in the hilarious severity assessment? The vulnerability is supposedly CRITICAL!!!!11!1!!one!, while description shows both a ridiculously small vulnerable population and ridiculously low impact. Population: a single, very old kernel version on a rare, outdated architecture, in one timezone only - and WHICH timezone! UTC+14 means just a couple of islands in the Pacific (Tonga, Kiribati...) - the probability of even one vulnerable system actually existing seems almost zero. Impact: the only possible consequence is switching from 12h to 24h (only in this direction)? This whole entry is very creative - just TRY to come up with a possible vulnerability (yes, it would classify as an actual vulnerability, why not?) that would have a LOWER severity than that...--162.158.91.89 13:41, 19 February 2018 (UTC)
- Agree Elektrizikekswerk (talk) 15:45, 19 February 2018 (UTC)
I think the article should start with an explanation of what is the CVE. From https://cve.mitre.org/
"CVE® is a list of entries—each containing an identification number, a description, and at least one public reference—for publicly known cybersecurity vulnerabilities. CVE Entries are used in numerous cybersecurity products and services from around the world, including the U.S. National Vulnerability Database (NVD)."
- -- Comment Police (talk) (please sign your comments with ~~~~)
"MySQL server 55.45" it is 5.5.45 if you zoom in a bit. 162.158.91.161 13:41, 19 February 2018 (UTC)Blocki
"An attacker can execute malicious code on their own machine and no one can stop them" might be a jab at the trend toward more closed systems, where even the owner of a device is limited in what they can do on it.
"A flaw in Mitre's CVE database allows arbitrary code insertion" could be meant as an explanation for the whole comic, i.e. those joke vulnerabilities were added to the CVE database using this flaw. 141.101.69.225 13:52, 19 February 2018 (UTC)
- Belatedly (thanks to the CAPTCHA problem), I see this as satirizing the attitude of some hardass computer security professionals who think no one, save themselves and certain highly trusted others, should be running malicious code on their own machines even if they aren't connected to the Internet and have no malicious intentions. Sort of like older cops who seethe that people out there are smoking pot or doing other drugs in the privacy of their homes and they can't do anything about that. Daniel Case (talk) 02:13, 30 May 2018 (UTC)
It's my first comment here, so I may be wrong. I see the "CRITICAL" as a "differential” joke exhibiting that the requirement standards may be very different from a constructor to another. In fact, it seems that the apple’s bugs described here (crash, fire, remote access granted) are the mosst critical ones. The only two concerning Linux are the one labeled as critical and the one about bribery. I don’t know what to think about the almost complete absence of windows though. Feriaman.
Could we get an Air Bud category? It seems to be a recurring theme in his comics. 162.158.246.88 18:50, 19 February 2018 (UTC)
- List of direct mentions of "air bud" in the explanations: 115:_Meerkat, 1439:_Rack_Unit, 1506:_xkcloud/Table_of_Permalinks, 1552:_Rulebook, 1819:_Sweet_16, 1957:_2018_CVE_List
- List of direct mentions of "air bud" in the transcripts: [None]
- Beep, boop, I'm not a bot. Fabian42 (talk) 20:41, 19 February 2018 (UTC)
Anyone happen to notice that instead of writing "mischievous," Randall opted for the non-standard spelling "mischevious?" The standard form would have been an I-before-E word... --162.158.88.164 00:45, 20 February 2018 (UTC)
"Diacritics are the accents found on letters in some languages (eg. č, ģ ķ, ļ, ņ, š, ž). These would not be found on emojis." This misses the point. There is nothing that stops a unicode emoji being followed by unicode combining diacritical mark. The rendering engine does not have to display this in any particular way, but catching fire would be considered a bug by must users.[citation needed] 162.158.74.213 03:35, 20 February 2018 (UTC)
"Flash was discontinued", really? Someone should tell Flash. And Facebook. I'm STILL experiencing issues on Facebook over their sloppy Flash programming interfering with my ability to watch Facebook videos (extra irritating as I'm sure my newly built computer is more powerful and capable than the computers owned by anyone I know, and certainly any phone or tablet, which don't experience these problems). And my last Flash update was a couple of weeks ago - seeing as this bug likes to include telling me I need to upgrade my Flash, even if I did so that day and Flash assures me I'm up date. NiceGuy1 (talk) 05:04, 20 February 2018 (UTC)
- Flash hasn't been discontinued, but I think one could call it deprecated. Adobe announced that they will stop updating and distributing Flash in 2020 so it will be "discontinued" in 2-3 years. Which means that if you're a web site owner, now's the time to migrate any Flash content to another platform (like HTML5/JavaScript). Additionally, most modern browsers make a point of disabling flash by default, forcing you to enable it on a per-site basis. Shamino (talk) 14:53, 20 February 2018 (UTC)
Timing Attack to exploit a race condition in garbage collection refers to Meltdown and Spectre CPU flaws that can be exploited in cloud server like the ones in Wikipedia.
I don't think this is correct. Garbage collection is a technique of freeing up memory no longer used by a program, completely unrelated to speculative execution and the Spectre/Meltdown exploits... Jaalenja (talk) 07:34, 20 February 2018 (UTC)
Apple products execute any code printed over a photo of a dog with a saddle and a baby riding it. ... This "bug" would not only require the device to figure out specifically what the photo contains image-wise, something that's REALLY HARD for computers to do reliably, it would also require OCR (Optical Character Recognition) type code to convert the text superimposed on the photo into executable code. In other words, it's hard to believe in 2018 that such a bug could exist. Maybe in the future when such things are more routine...? ...
The funny thing is that I don't think it's beyond the realm of plausibility. Given the fact that modern operating systems try to index as much as possible, for faster searches, it seems logical that some OS (if not now, then in the future) would try to run OCR against every image and video in order to index whatever text it finds (much like how YouTube auto-generates captions by running speech-recognition over the entire soundtrack). Ditto for more generic image recognition to identify and index the picture content. A system that does this could easily end up with a bug (or back door) where certain kinds of image content result in an attempt to execute its OCR results as code. Shamino (talk) 15:03, 20 February 2018 (UTC)
Does anyone think the 'I before E' could be a stab at Apple, in reference to Internet Explorer? -- Comment Police (talk) (please sign your comments with ~~~~)
While it is true that part of the plot of the movie "Air Bud" was that there was nothing in the rules to prevent a dog joining a basketball team, I suspect that the recent attempt to run a dog as candidate for governor of Kansas was more on Randal's mind than a 20+ year old movie that (at most) a few million people saw when it was released.162.158.78.16 05:27, 22 February 2018 (UTC)
- Actually, I find AirBud has become more of a thing to reference than a movie to watch. I believe the idea has been recycled a few times (a dog playing football, I think a dog playing baseball), yet it's AirBud, the original, that's always getting referenced (okay, "always" is an overstatement, but still). At the very least I know Randall has referenced it a few times, sometimes by name, enough times that I'd say it's safe to say AirBud is on his list of favourite references. If anything, this dog governor sounds obscure enough that he may not have heard about it, making the AirBud reference more likely, though being wacky politics I wouldn't be surprised if he's well aware, either. :) NiceGuy1 (talk) 04:49, 23 February 2018 (UTC)
Is it just me, or does it feel like the "hack via edit box" thing feel like a reference to us? I mean, not only can this site be added to like that, it's the only one I know of and visit where you can do so without having an account. Seems perfect as the target of that particular one. :) NiceGuy1 (talk) 04:55, 23 February 2018 (UTC)
- The only one? So I guess you don't go on wikipedia much. --Quantum7 (talk) 08:49, 23 March 2018 (UTC)
Is it notable that the bugs gradually become more and more trivial except where an Apple device is involved, where they progressively get both more worrying and more impossible to accomplish? 108.162.221.95 05:37, 23 March 2018 (UTC)
